EventLog Analyzer Platform
Accelerate Your Log Analysis Process and Get Ahead of Threats with GOIP EventLog Analyzer
See how EventLog Analyzer helps you with complete
Windows event log management.
When it comes to Windows devices, dealing with the terabytes of event log data they generate can be a hassle. With EventLog Analyzer, a powerful event log management tool that provides end-to-end event log management, security admins can automate processes, including collecting logs in the network and archiving those logs at a predetermined time.
Our Features and Capabilities:
Unlocking Your Business Potential

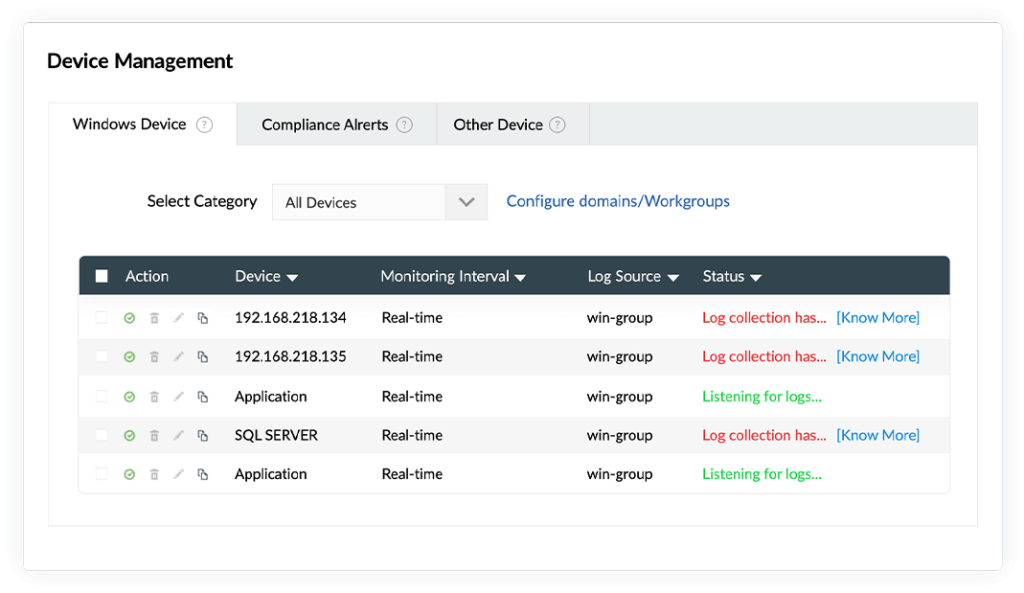
An important function of an event log management tool is collecting event logs from every source possible. EventLog Analyzer‘s event log collection capabilities are exceptional with support for both agentless and agent-based methods of log collection.
Agentless event log collection
This method involves collecting event logs using native mechanisms in Windows devices. EventLog Analyzer can communicate with the Windows devices in your network and collect event logs via mechanisms such as WMI, DCOM, and RPC.
Agent-based event log collection
During situations where native mechanisms are unable to be used for log collection, EventLog Analyzer comes bundled with an event log collecting agent. This agent needs to be installed in the log source in order to communicate with and deliver event logs to EventLog Analyzer‘s server.

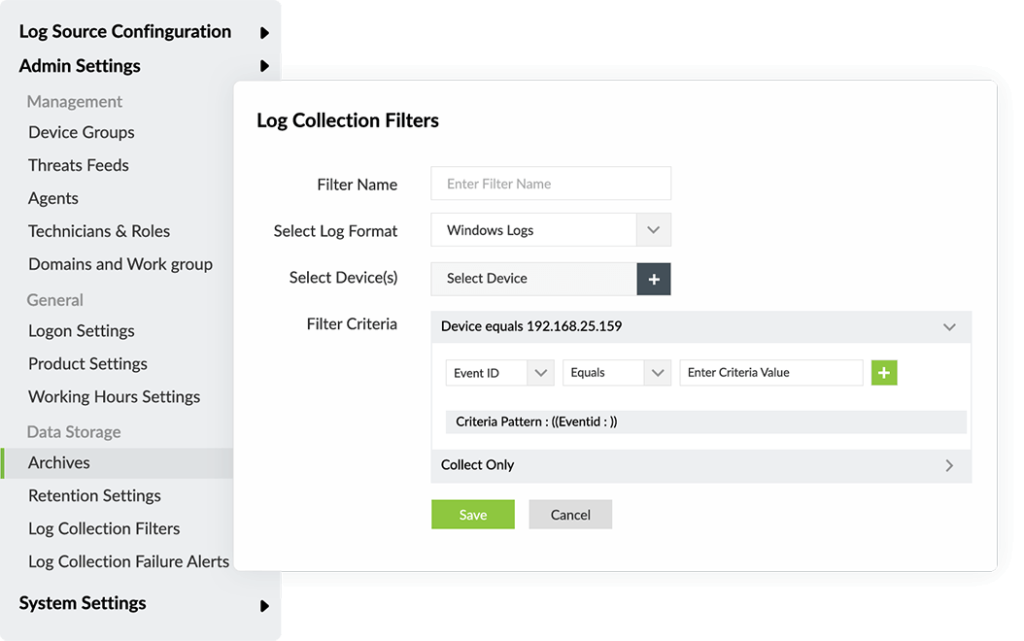
Event log filters
Most of the event logs generated in a network denote routine activities.
This presents two challenges:
Spotting event logs that provide security information.
Maintaining the required storage space for saving all the collected event logs.
To address these challenges, EventLog Analyzer provides event log filters, which can be used to sort through the collected logs to find those that are significant from a security perspective. These customizable filters are based on the event log source, user, or components of the log. All event logs can be archived automatically for future reference through EventLog Analyzer.

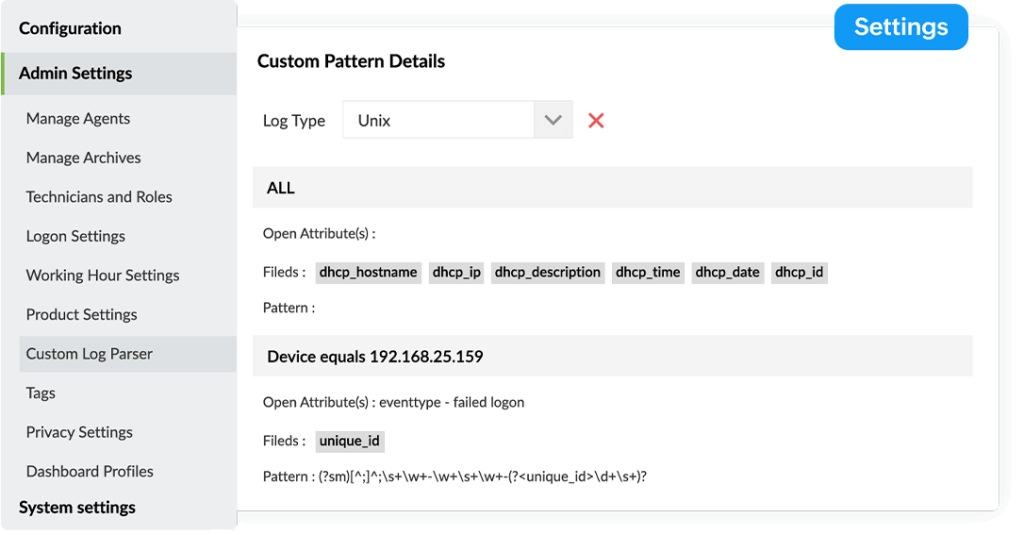
To gain the most from the collected event logs, it’s vital for a log management tool to parse event logs. EventLog Analyzer has a built-in event log parser that can normalize, parse, and index event logs.
Understand parsing through an example
Let’s take a log with a device name and user name in it; while this information is readily available, it’s not clear which name is for the device and which is for the user.
EventLog Analyzer‘s event log parser breaks event logs down so that different pieces of information—for this example, the device name and username—each appear as their own logs, which are then grouped into the appropriate sections.

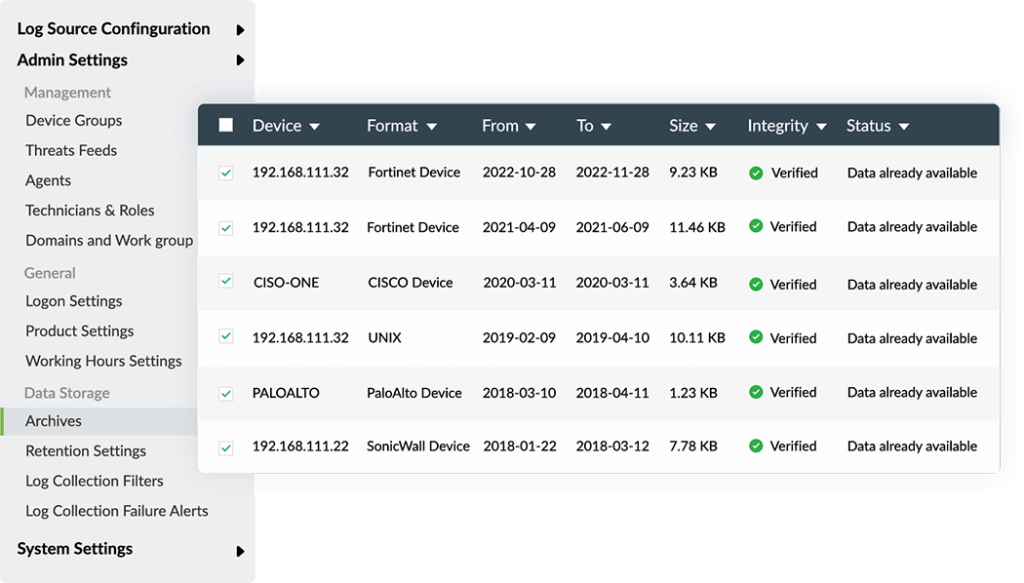
Archiving and properly disposing of collected event logs is an important part of the event log management cycle. Additionally, major IT security regulatory agencies scrutinize the process organizations have for event log archival. Most of them mandate the number of days event logs need to be stored, before the logs can be permanently deleted.
By deploying EventLog Analyzer, organizations can automate event log archiving. You can designate the number of days after which the collected event logs will be moved to the archive, and customize the number of days after which the archived event logs are permanently deleted.
These values can be decided based on the compliance mandates and internal audit requirements that your business needs to comply with. EventLog Analyzer’s event log archival feature will help enterprises comply with all major IT mandates such as HIPAA, SOX, GLBA, PCI DSS, and GDPR.
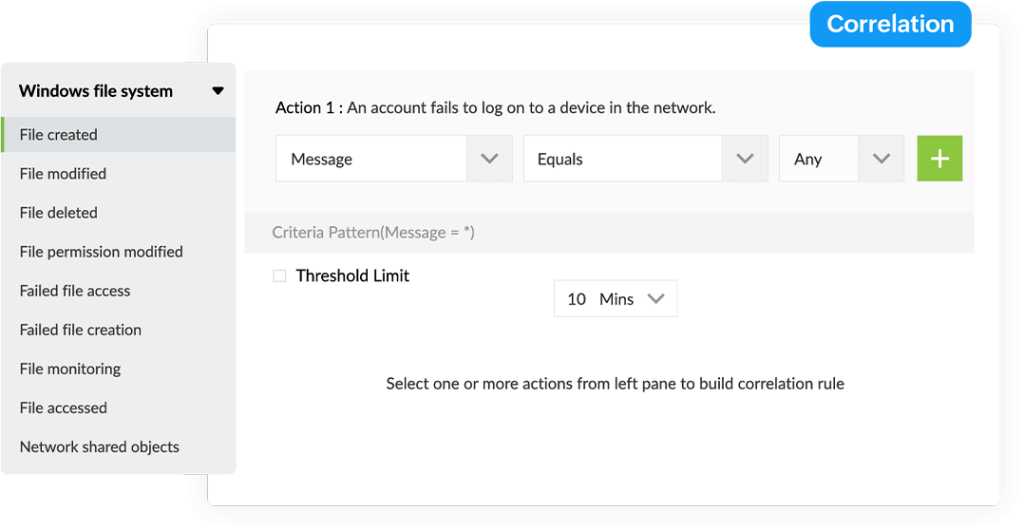

Log analysis is important for an event log management tool to perform as an efficient security tool . EventLog Analyzer expedites event log analysis with its log parser. This is further strengthened by EventLog Analyzer’s correlation engine.
EventLog Analyzer’s correlation engine can save you from the painstaking process of manually correlating log data by automatically retrieving event logs from its database and comparing them with formatted logs from other sources.
This will help with detecting any chain of events that might represent an attack on the network.
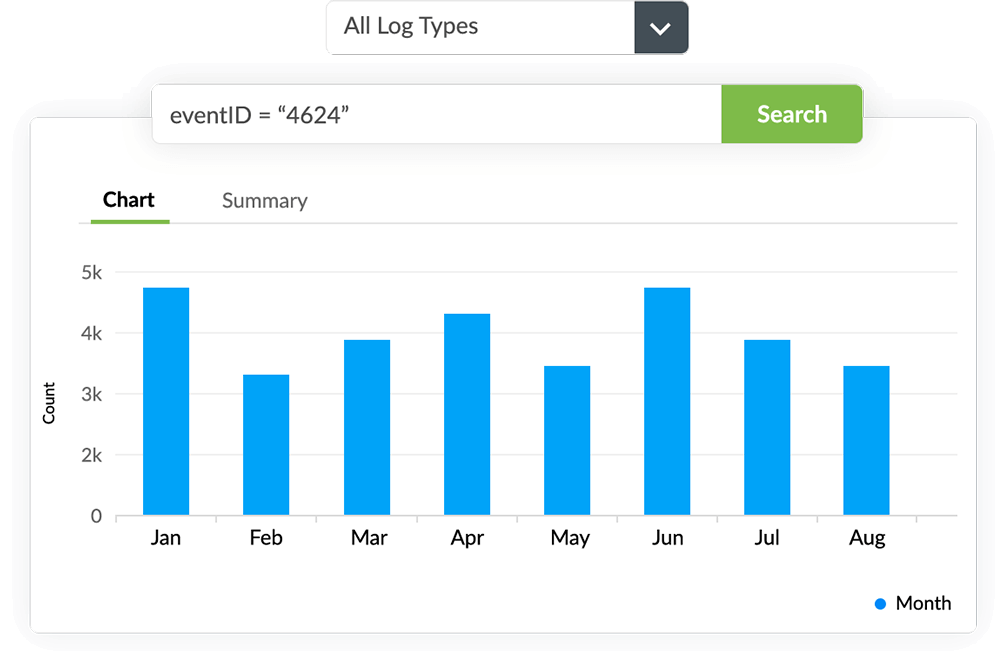

IT administrators often need to perform forensic log analysis in their organization. During forensic log analysis, administrators have to search through logs to find the information they need, but the enormous volume of event logs generated by Windows devices makes searching these logs manually almost impossible.
EventLog Analyzer has a dedicated search module that is easy to learn and use. It supports search queries containing wildcards and Boolean operators; you can also perform grouped and range searches.
To search for an event log using EventLog Analyzer, you can utilize continuous prompts to frame a logical query and this tool will render all the logs that match that your query.
5 reasons
to choose EventLog Analyzer
Processes log data at 25,000 logs/second to detect attacks in real time and conduct quick forensic analysis to reduce the impact of a breach.
Collects, analyzes, correlates, searches, and archives log data from over 700 log sources. Includes a custom log parser to analyze any human-readable log format.
Meet regulatory compliance requirements with predefined compliance reports for PCI DSS, FISMA, GLBA, SOX, HIPAA, ISO 27001, and more.
and mitigation
Uncover security threats with advanced threat detection mechanisms, such as event correlation and threat feed analysis, and mitigate them using automated workflows.
Audits network perimeter devices’ logs, user activities, server account changes, user accesses, and a lot more to meet security auditing needs.
Download Useful Resources
Did you know
Our IP backbone is ranked #1 worldwide?
OUR Certifications and Accreditations
These certifications enhance our capabilities and ensure we meet the highest standards in delivering innovative solutions to our clients.

Penetration Testing Service Licence & Managed Security Operations Centre (SOC) Monitoring Service Licence 
Singapore SBO IMDA 
HK SBO OFCA 
ISO 27001 
ASP(MCMC) 
FCC 214 & FCC 499
CCIE
Cisco Certified Internetwork Expert
CISSP
Certified Information System Security Professional
LPIC
Linux Network Professional Certification
MCSE
Microsoft Certified Solution Expert
PMP
Project Management Professional
HCNA HCNA – R&S HCNA – STORAGE
Huawei Certified Network Associate
ACP
Alibaba Cloud Certified Professional
ACA
Alibaba Cloud Certified Associate
AWS ASSOCIATES
Certified Solutions Architect

Contact Our Experts for
a Free Consultation
Ready to elevate your business with GOIP Group’s services?
by calling (65) 6011 6288 or emailing info@goipgroup.com.
Discover tailored solutions and insights that can drive your success.
